How can you establish 360 Degree Protection around your data?
- Identify focus areas for security
- Address Concerns Surrounding Data Availability
- Retain Data Integrity with Object Storage
In today’s current digital landscape, businesses are increasingly relying on cloud technologies and IoT devices to improve efficiency and scalability.
Every one of your employees needs instant access to business information required to execute their workflows. However, the more IoT devices, endpoints, and cloud technologies a company integrate into its operations, the more vulnerable it becomes in terms of asset security.
This has made it necessary for every company, large or small, to establish a 360 Degree Protection approach to protect their networks, data, and assets from all types of threats.
In this blog post will give you a rundown on how to do it:
1. Identify focus areas for security
Building Blocks of Data Security when Transitioning to Cloud Computing
While cloud security may pose a challenge to your resources, you’ll need to ensure you still get the essentials right before starting any transition. A 360° security plan requires a solid foundation that can scale with your teams going forward.
To successfully transition operations securely, you should consider starting a pilot project after you’ve set out your cloud governance strategy and identified the focus areas you need to readdress. Regardless of your technology stack, you’ll still want to focus on:
- Device and user authentication – Network Access Control (NAC) solutions should provide you with complete transparency over every connected device. Before authenticating any device, you’ll need to perform a policy compliance inspection and 2-Factor Authentication (2FA) or Multi-Factor Authentication (MFA), where possible.
- Data and system availability – Disaster recovery and Data Loss Prevention (DLP) planning should address all the risks posed to your data in transit (networks), rest (storage), and access (endpoints).
- Monitoring and oversight – You’ll still need to monitor all traffic and access to sensitive data. Selective content scanning can help you identify threats early and respond effectively without compromising network performance.
The next step is to establish a 360° view of your threat landscape and build a data protection framework that covers three key factors, namely data availability, data integrity, and data security.
2. Addressing Concerns Surrounding Data Availability
When considering on-premises vs. on-cloud deployments, your data still needs to be available and provide your teams with maximum uptime. Failover, backup, and replication processes are easier in the cloud, but only when planned for adequately. Disaster recovery planning should include considerations like:
- Clear objectives – You’ll want to establish your current baseline and then set your team’s Recovery Time Objective (RTO) and Recovery Point Objective (RPO). These metrics will help you establish an adequate time to recover from a data loss incident and to which point you can return it.
- Failover and failback procedures – Failover considers redundancy issues to ensure business continuity in the event of a loss of service from one location to another. Failback is your ability to switch back to original systems in the event of a complete loss of access.
- System restores – Recovering from a user error in a specific application or system requires returning to restore point from a scheduled backup. Coordinating these tasks with cloud-service providers could be more complex than a generalist IT resource is capable of handling.
Data availability ultimately relies on your teams’ ability to respond to any event where operations will be impacted due to a loss of data or services. Your plan should mitigate all the risks a rapid deployment could lead to by considering DLP and failover backup while providing dynamic access to your company networks.
Retaining Data Integrity with Object Storage
One major element you’ll want to consider is the difference between block storage and object storage. Storage Area Networks (SANs) save data in blocks, making them popular in enterprise environments due to the low latency and flexibility with business-critical applications.
Object storage creates data objects that include metadata and stores it in a flat structure with an object ID. It’s popular in cloud storage environments as all data resides in a single repository, retrievable by a sequence of IDs instead of constructing a complex query. Object Storage Solutions (OBS) overcomes the challenges of traditional data storage techniques, making it suitable for:
- Rateless Erasure Coding – Increases the consistency and accuracy of restored data compared to RAID systems.
- Reducing recovery times – Object availability and restoration are quicker as OBS doesn’t require restoring volumes by blocks.
- Improved data Integrity - It also improves validation processes when assessing data integrity and increases availability using an erasure-coded environment.
Legacy systems relied heavily on block storage solutions to remain efficient and secure in enterprise environments. Keeping data secure while transitioning to a hybrid cloud deployment will require additional planning for changes in how you protect your data using different storage technologies.
Tips for Elevating Data Security While Granting Access from Anywhere
Whatever the business motivations are, transitioning to the cloud requires a concise approach to data security before moving forward with a full-scale implementation. You’ll need to consider all factors that affect your data protection, including monitoring all connected devices and addressing IoT security.
The top five ways to prevent data theft are:
- Reduce reliance on paper files and documents and ensure you shred all sensitive information before recycling.
- Restrict all access to sensitive data.
- Implement strong password policies on all your computers and devices.
- Enable firewalls on all your digital equipment.
- Deploy threat detection solutions including anti-virus and anti-spyware on every connected device.
Symantec predicts that by the end of 2020, there will be 200 billion connected devices around the globe. For traditional IT security teams, this is an exponential expansion of the attack perimeter and needs an adequate strategy to ensure a safe transition.
The same data security and DLP considerations still apply, which include:
- Preventing device theft – All encryption protection can be rendered obsolete if a device is lost or stolen. Adopting the appropriate security policies will prevent a stolen device from leading to a breach.
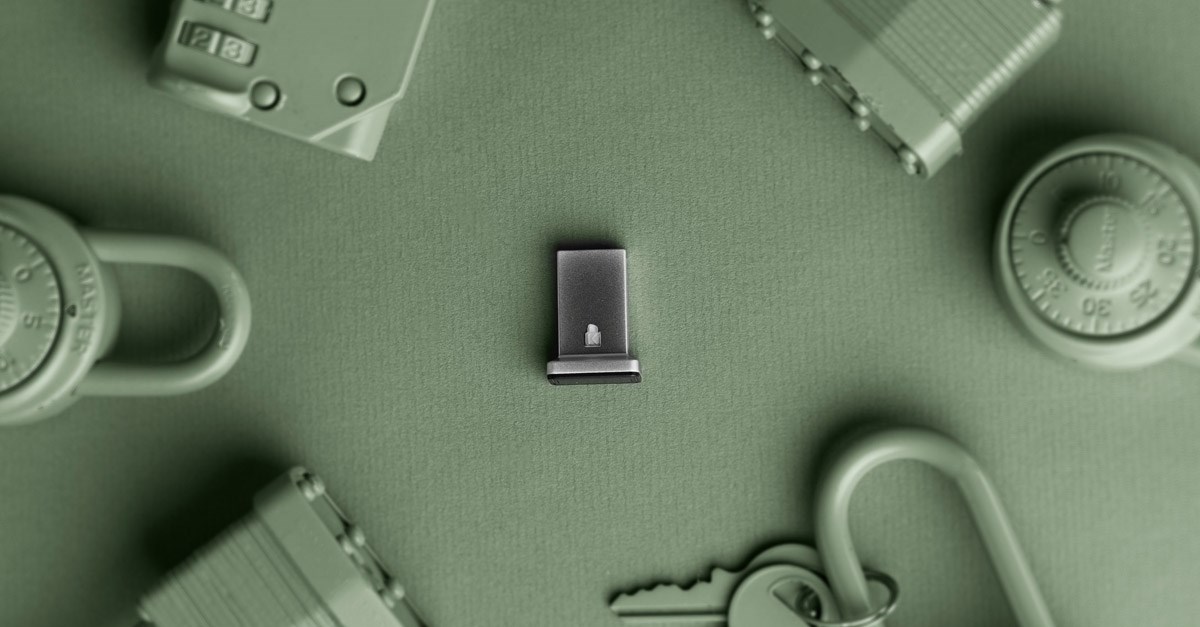
- Using 2-Factor Authentication (2FA) and Multi-Factor Authentication (MFA) – Biometric fingerprint scanners add an additional layer to device and application security. Opt for solutions that use FIDO and FIDO2 certified technologies.
- Deploy policies for all endpoint devices – Regularly scan endpoint devices using a cybersecurity threat scanner, while requiring a Virtual Private Network (VPN) to access sensitive files and folders from outside the company network. Endpoint security remains one of the core data protection principles required with cloud adoption and digital transformation.
- Consider insider threats – Device theft doesn’t necessarily require someone from outside the organization to penetrate your perimeter. You should also consider insider threats, requiring you to secure all devices physically in the office.
Any security system is only as strong as its weakest link, and IoT devices have been found to have numerous vulnerabilities.
- The good news is that there are several strategies that can help you take measures towards increasing your organization’s security and increasing the integrity of your data. By combining all three levels of security – Physical, Logical, and Operational with a 360 approach – you can reduce the risks to your IoT deployments.
Shop Now for Kensington Security Products
Establishing 360° Security with Kensington Data Protection Solutions
Changes to the way your employees access and interact with your business information will add additional complexity to your cybersecurity perimeters. You’ll want to understand what risks any transition poses and where you’ll need to deploy additional protection to secure your company networks.
Secure your devices and applications with Kensington biometric authentication solutions.
