One Lock for Any Slot
Fits standard, nano, or wedge-shaped laptop security slots, regardless of brand or generation, helping to “future-proof” your locking solution. Lock tips are easily changed; a tether keeps unused lock tips handy.






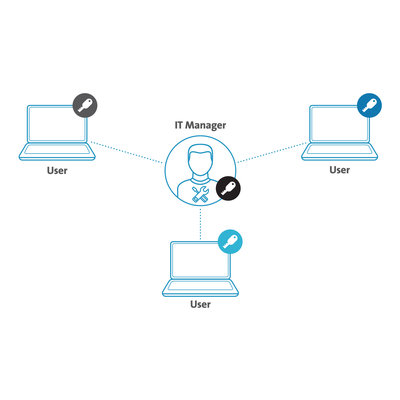


Now there’s one keyed cable lock that secures it all. The Universal 3-in-1 Keyed Laptop Lock fits any laptop security slot — standard, nano, and wedge-shaped — helping to “future-proof” your locking solution. Lock tips are easily changed; a tether keeps unused lock tips handy. Common 5mm keying system, patented Hidden Pin™ technology, and carbon steel cable provide strong security against picking and theft attempts. Pivot and rotate lock head allows flexible movement and easy key insertion. Additional features include Register & Retrieve™ for quick, secure, and easy key replacement; master keyed for administrative access; and a five-year warranty backed by Kensington, inventor and worldwide leader in laptop security locks. All Kensington locks are verified and tested for strength, physical endurance, and mechanical resilience.