Thunderbolt™ 5 Docking Station
Seamless multi-monitor setups, 80Gbps transfers, 120Gbps bandwidth boost, and 140W power delivery.
Shop Now

Seamless multi-monitor setups, 80Gbps transfers, 120Gbps bandwidth boost, and 140W power delivery.
Shop Now


In an age where criminals can learn how to break and pick locks online, Kensington continues to stay ahead of the curve, offering more advanced security options than anyone.
Request Business Pricing
Laptops are getting thinner and lighter. However, mobility comes with compromise. Reducing the size of a portable device chassis often means reducing the number of ports available for connectivity or removing the security lock slot. We are constantly looking at ways to help organizations keep their hardware, and the information contained on it, safe.
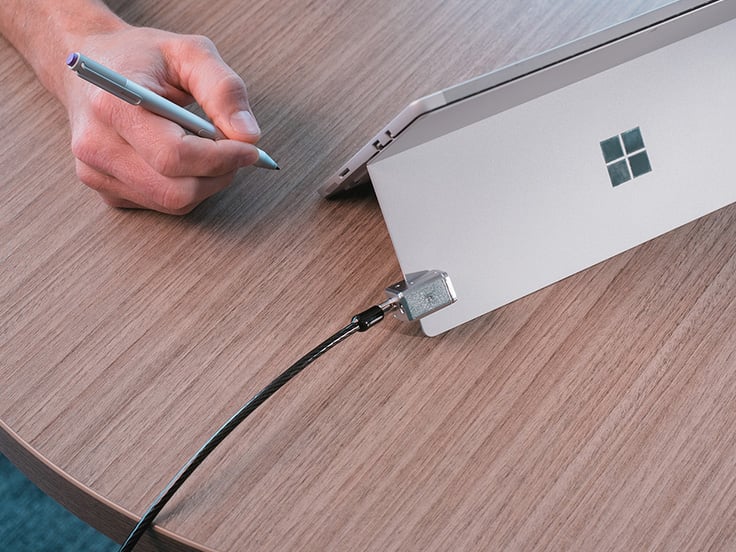
Another trend in the market is the increased use of tablets as a primary computing device. The additional mobility of these devices makes them even easier to grab. Until now.

Why stop at the lock? Adding 2FA to a mobile device makes it even harder for the wrong person to access valuable data.

In some high risk environments, ports can be a vulnerability that must be guarded. Kensington provides USB security locks to ensure data can’t be removed or malicious code added.