
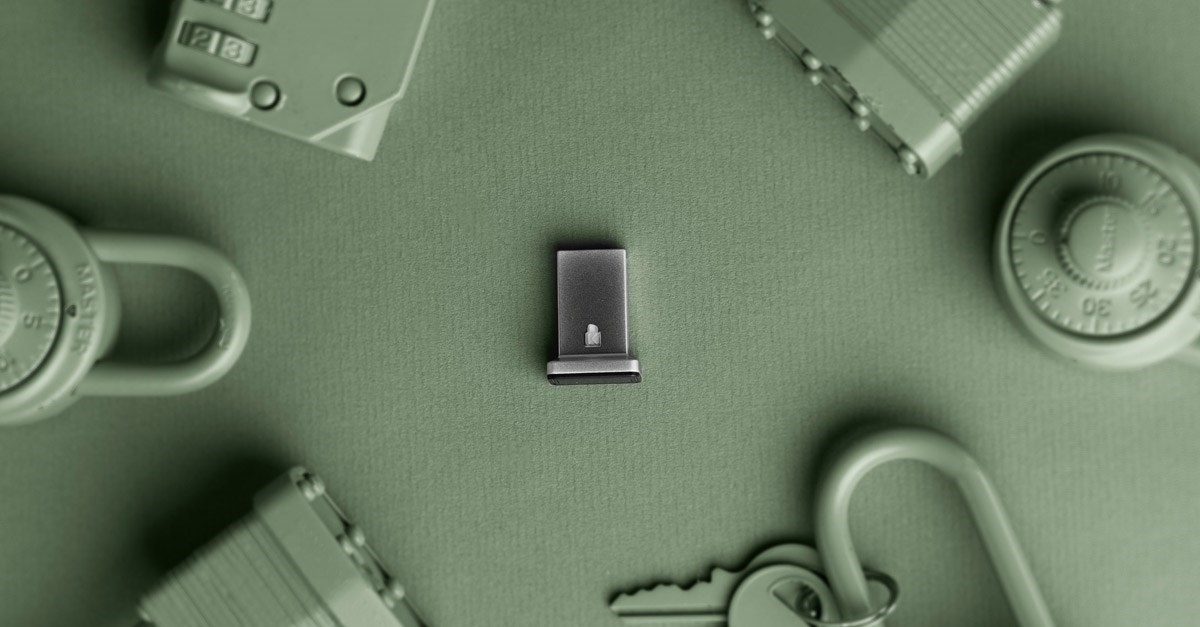
In today's rapidly evolving digital world, cyber threats and attacks are more prevalent than ever before. According to CISA, an agency of the U.S. Department of Homeland Security, the aggregate impact of cybercrime at the national level in 2020 was approximately $243 billion annually, rising to more than $1 trillion annually for the most extreme set of assumptions. As a result, IT managers and business owners are under increasing pressure to secure their network environment and protect their organization's sensitive data from cyberattacks. One effective way to mitigate these risks is with security keys
This article will provide a comprehensive guide to security keys and terms, explaining the key concepts and terminology that IT professionals need to know to secure their network environment against cyber threats. We will review:
1. Understanding Security Keys
2. Primary Functions of Security Keys
3. The Importance of Authentication
4. Definition and Benefits of Two-Factor Authentication (2FA)
5. Certificate Issuance Process and Validation
6. Secure Socket Layer (SSL)/Transport Layer Security (TLS)
7. Types of Hardware Security Keys (USB, NFC, Bluetooth®)
8. Compatibility with Devices and Platforms
9. Security Certifications and Standards
By the end, you will have a better understanding of the key terminology and concepts related to security keys and be equipped with the knowledge you need to make informed decisions about how to secure your network environment against cyberattacks.
Understanding Security Keys
Security keys are a critical component of any comprehensive cybersecurity strategy. They are used to authenticate and authorize access to a computer system, network, or data. Security keys play a crucial role in protecting sensitive information from cyber threats and attacks by ensuring that only authorized individuals can access the data. These keys come in various forms, from physical security keys to software-based solutions.
Software-based security keys are typically built into a device's operating system, web browser, or other software. These keys may be more convenient than physical security keys, but they are also more vulnerable to cyberattacks since they can be compromised by malware or other types of malicious software.
Physical security keys, on the other hand, are typically small USB devices that plug into a computer's USB port and provide an additional layer of authentication and authorization. Physical security keys are highly secure and resistant to cyberattacks since they are not vulnerable to phishing or other types of social engineering attacks. However, physical security keys can be lost or stolen, and they require additional hardware.

Primary Functions of Security Keys
Security keys are used to perform three primary functions: encryption, authentication, and authorization. Encryption involves converting information into an unintelligible form, ensuring that only authorized individuals can access the data. Authentication involves verifying the identity of a user or device, typically through a password or biometric identifier such as a fingerprint. Authorization determines what level of access a user or device has to a system or network, ensuring that only authorized individuals can perform certain actions or access specific data.
The Importance of Authentication
Authentication is a critical component of any cybersecurity strategy since it ensures that only authorized individuals can access the data. Without proper authentication, cybercriminals could gain access to sensitive information, causing significant damage to an organization. There are various authentication methods, including passwords, biometric identifiers, and security keys.
Definition and Benefits of Two-Factor Authentication (2FA)
Two-Factor Authentication (2FA) is an authentication method that requires two distinct forms of identification before granting access to a system or network. This method is more secure than a single-factor authentication method since it requires two separate pieces of information to gain access. The benefits of 2FA include increased security, reduced risk of data breaches and cyberattacks, and enhanced user trust and confidence.
Certificate Issuance Process and Validation
Certificate issuance and validation are critical components of any organization’s cybersecurity strategy. The certificate issuance process involves issuing digital certificates to individuals or organizations to verify their identity and establish trust. Validation involves verifying that a certificate is valid and has not been tampered with or compromised.
Secure Socket Layer (SSL)/Transport Layer Security (TLS)
Secure Socket Layer (SSL) and Transport Layer Security (TLS) are two widely used encryption protocols that provide secure communication over the internet. These protocols are used to encrypt data, ensuring that only authorized individuals can access the data.
Types of Hardware Security Keys (USB, NFC, Bluetooth®)
Hardware security keys are physical devices that provide an additional layer of authentication and authorization. There are various types of hardware security keys, including USB, NFC, and Bluetooth®. These keys are highly secure and resistant to cyberattacks since they are not vulnerable to phishing or other types of social engineering attacks.
Compatibility with Devices and Platforms
Compatibility is a critical consideration when selecting a security key. Different security keys may be compatible with different devices and platforms, and it's essential to ensure that the key you choose is compatible with your organization's systems and devices.
Security Certifications and Standards
Security certifications and standards are essential for ensuring that a security key is secure and reliable. There are various security certifications and standards, including FIDO2™, FIPS, and Common Criteria. These certifications and standards provide organizations with the assurance that the security key they are using meets industry standards for security and reliability.
Key Management Practices
Effective key management practices and procedures are critical for protecting sensitive information in an organization. Backup and recovery strategies, key rotation, and key revocation procedures are essential components of key management and should be implemented to mitigate the risk of cyber threats and ensure the security of sensitive information.
Glossary of Terms
To help you understand the technical language around security keys, we have compiled a comprehensive glossary of key terms and definitions.
Attestation: The process in which the security key provides proof of its authenticity to the relying party (e.g., a website or service). Attestation ensures that the security key is genuine and not a malicious or counterfeit device.
Authenticator Attachment: Refers to the physical connection method used to connect the security key to the client device. Common attachment types include USB, NFC (Near Field Communication), and Bluetooth®.
Credential: A digital representation of a user's identity used for authentication. In the context of FIDO® security keys, the credential is typically a public-private key pair generated during the registration process.
CTAP and CTAP2: The acronym for Client-to-Authenticator Protocol. The protocol used for communication between the client device (such as a computer or smartphone) and the authenticator (security key). CTAP facilitates the registration and authentication process, ensuring secure and reliable communication. CTAP2 (Client to authenticator protocol) is the protocol to secure device-to-device communication with authenticators and FIDO2 enabled browsers and OS to enable passwordless, second factor or multifactor authentication.
FIDO: The acronym for Fast Identity Online. An open authentication standard developed by the FIDO Alliance to provide strong, passwordless authentication. FIDO enables password-only logins to be replaced with secure and fast login experiences across websites and apps via fingerprint, facial recognition, security keys, or voice.
FIDO Alliance: An industry consortium consisting of major technology companies and organizations that collaborate to develop and promote open authentication standards, including FIDO2.
FIDO2: The second generation of the FIDO standard, which includes the Web Authentication (WebAuthn) and Client-to-Authenticator Protocol (CTAP). FIDO2 enables passwordless authentication and is supported by various platforms and browsers. It enables secure, passwordless authentication using a fingerprint reader or camera.
Public Key Cryptography: A cryptographic system that uses a pair of mathematically related keys: a public key and a private key. The public key is shared openly, while the private key is kept secret. FIDO security keys use public key cryptography to securely authenticate users.
Relying Party: The entity (e.g., a website or service) that relies on FIDO based authentication to verify the user's identity. The relying party interacts with the security key during the authentication process.
Resident Key: A type of credential stored on the security key itself, allowing the user to authenticate without relying on a separate device or server. Resident keys are particularly useful for offline or remote scenarios.
Roaming Authenticator: A security key that can be used with multiple devices or platforms. Roaming authenticators allow users to carry a single security key and use it across different devices for authentication.
Security Key: A physical device, often in the form of a USB dongle, that is used for FIDO based authentication. It contains cryptographic keys and performs cryptographic operations to securely verify the user's identity.
Self-attestation: A method used by security keys to provide attestation information without relying on an external attestation authority. Self-attestation is typically used by simpler and lower-cost security key models.
U2F: The acronym for Universal Second Factor. U2F is the authentication standard for two-factor authentication where one factor is a device such as a key, token, or card and the other factor is a username and password.
User Verification: The process of confirming the user's identity during authentication. FIDO security keys support various user verification methods, such as biometrics (fingerprint or facial recognition) or PIN entry.
Web Authentication (WebAuthn): A web standard developed by the World Wide Web Consortium (W3C) and adopted by FIDO2. WebAuthn allows web applications to integrate FIDO2 authentication methods and provides a standardized API for interacting with security keys.
Conclusion
Protecting sensitive information is critical to the success of any organization. Security keys can play a vital role in ensuring the security and integrity of data, systems, and networks. They provide a robust and scalable method for authentication, authorization, and encryption, helping to mitigate the risks posed by cyber threats.
As discussed, security keys come in various forms, from physical devices to software-based solutions, with each type offering its advantages and limitations. Key management practices such as backup and recovery strategies, key rotation, and key revocation procedures are essential for effective security key deployment, ensuring that only authorized individuals have access to sensitive information.
With the ever-increasing sophistication of cyber threats, it is essential to stay up to date with the latest advancements in security key technology and best practices. By implementing security keys and key management practices, organizations can create a robust and secure environment to protect sensitive information from cyber threats and make informed decisions about how to integrate security keys into their cybersecurity strategy to safeguard their data and networks against potential attacks.
Kensington offers a line of world-class biometric security products that provide substantially higher assurance for regular consumers and enterprise customers. Our VeriMark™ product family is built on SentryPoint, an industry-leading suite of security features for Synaptics’ fingerprint sensor that incorporates several key market differentiators. If you are ready to secure your enterprise IT infrastructure but are unsure of the best way to protect your users, our team is here to help.
Learn more about Kensington’s fingerprint and security keys
